Ledger Live Login — Ultimate Guide to Safe Access, Hardware Security & Self-Custody Mastery
Dive into a comprehensive, beginner-friendly explanation of Ledger Live login mechanics, hardware wallet protection, cold storage principles, and scam avoidance — written to help you retain full control over your crypto assets.
Why Secure Login Is the Backbone of Self-Custody
Owning cryptocurrency means owning your keys — and with ownership comes responsibility.
Ledger Live serves as your control panel, but the real defense lies in the hardware wallet itself.
Attackers exploit human behavior more than technology: imitation websites, cloned login portals, and social engineering campaigns target users who are unfamiliar with the correct workflow.
Understanding the mechanics behind **private keys, transaction signing, cold storage, and Web3 interaction** helps you avoid these traps entirely.
This guide explains not just how to log in, but why the process protects your funds at every layer.
Ledger Live serves as your control panel, but the real defense lies in the hardware wallet itself.
Attackers exploit human behavior more than technology: imitation websites, cloned login portals, and social engineering campaigns target users who are unfamiliar with the correct workflow.
Understanding the mechanics behind **private keys, transaction signing, cold storage, and Web3 interaction** helps you avoid these traps entirely.
This guide explains not just how to log in, but why the process protects your funds at every layer.
What Ledger Live Actually Provides
Ledger Live acts as a dashboard for:
The signing process is performed offline, which is why Ledger remains one of the most trusted self-custody solutions in the industry.
- Viewing asset balances
- Sending and receiving transactions
- Installing firmware updates
- Connecting to DeFi platforms
- Managing multiple blockchain accounts
The signing process is performed offline, which is why Ledger remains one of the most trusted self-custody solutions in the industry.
The Phishing Trap That Almost Worked
Maya typed “Ledger Live login” into a search engine and clicked a slick-looking page.
The interface requested that she “connect the device and confirm seed words.”
Something felt wrong — because every authentic Ledger flow keeps backup phrases offline.
She closed the page, checked the official domain, and avoided a catastrophic theft.
**Phishers rely on urgency and familiarity. The correct knowledge breaks their strategy.**
The interface requested that she “connect the device and confirm seed words.”
Something felt wrong — because every authentic Ledger flow keeps backup phrases offline.
She closed the page, checked the official domain, and avoided a catastrophic theft.
**Phishers rely on urgency and familiarity. The correct knowledge breaks their strategy.**
Ledger Live Login — Secure Workflow
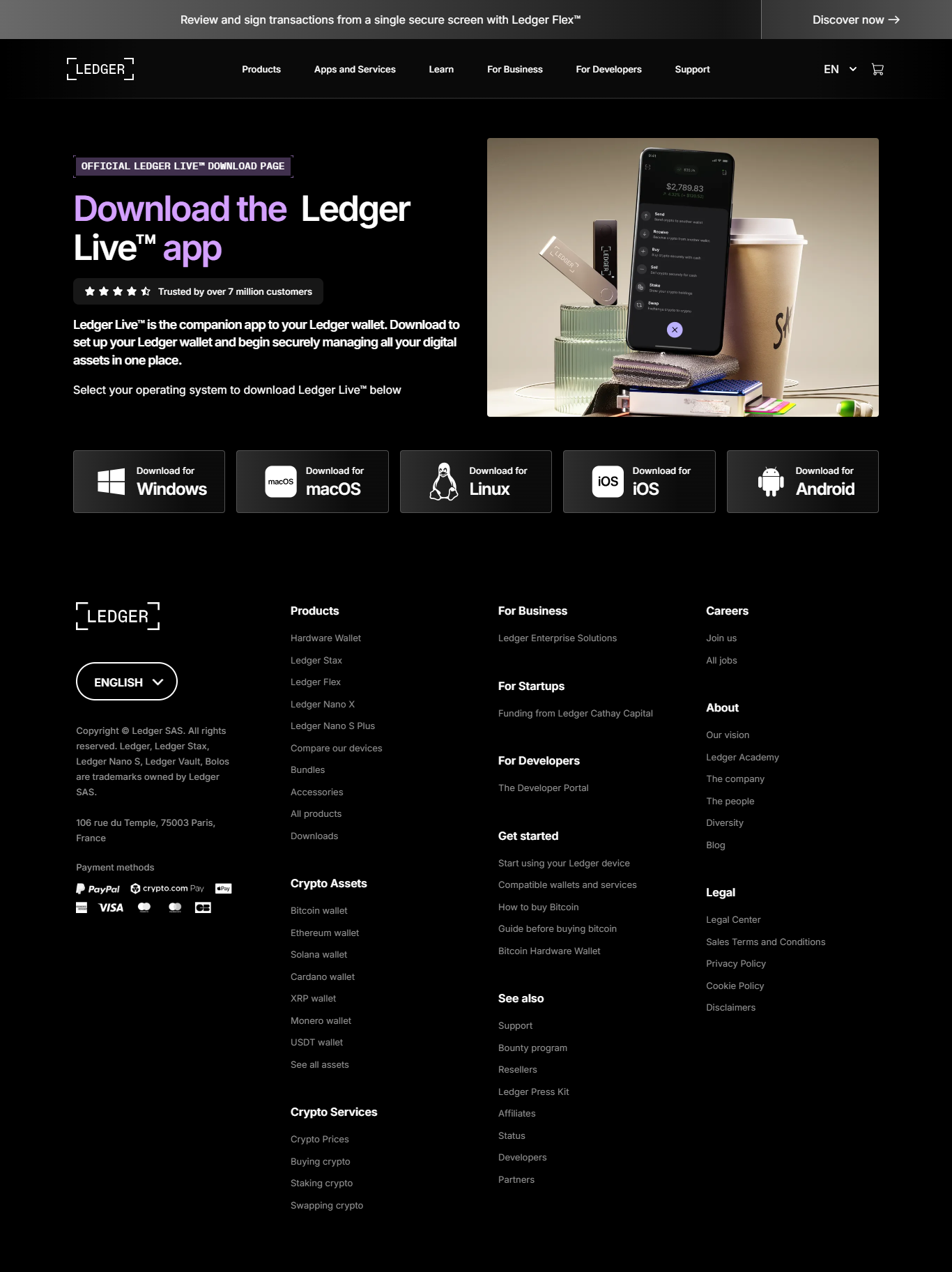
1. Download Ledger Live Only From the Official Site
Search results often feature paid ads from scammers.
2. Install and Open the Application
Ledger Live is available across major platforms.
3. Connect Your Ledger Device
USB for Nano S/S Plus — Bluetooth for Nano X.
4. Enter Your PIN On the Hardware Device
The PIN never touches your computer or browser.
Understanding Ledger Security Architecture
Ledger devices combine multiple layers:
Concepts such as **private key custody, blockchain immutability, and transaction validation** work together to create a secure environment for digital assets.
- Secure element chips resistant to tampering
- Offline transaction signing
- Physical screen verification
- Cold storage isolation
Concepts such as **private key custody, blockchain immutability, and transaction validation** work together to create a secure environment for digital assets.
Wallet Security Comparison
| Wallet Type | Security Level | Key Control | Ideal For |
|---|---|---|---|
| Ledger Hardware Wallet | Very High | User | Long-term storage |
| Mobile Wallet | Medium | User | Everyday use |
| Exchange Wallet | Low | Exchange | Trading |
Core Security Principles
✔ Use only official Ledger software
✔ Never enter your recovery phrase online
✔ Keep backups offline and secure
✔ Authenticate transactions on the device
✔ Avoid unknown plugins or “support” pages
✔ Update firmware regularly
✔ Never enter your recovery phrase online
✔ Keep backups offline and secure
✔ Authenticate transactions on the device
✔ Avoid unknown plugins or “support” pages
✔ Update firmware regularly
Frequently Asked Questions
1. Does Ledger Live store my keys?
No — keys remain inside the hardware wallet.
2. Does it require a password?
No — only a PIN entered on device.
3. Can it be hacked?
Not in a way that reveals keys, because signing remains offline.
4. Does it support many cryptocurrencies?
Yes — thousands across multiple networks.
5. What if I lose my device?
Restore using the recovery phrase on a new Ledger.
No — keys remain inside the hardware wallet.
2. Does it require a password?
No — only a PIN entered on device.
3. Can it be hacked?
Not in a way that reveals keys, because signing remains offline.
4. Does it support many cryptocurrencies?
Yes — thousands across multiple networks.
5. What if I lose my device?
Restore using the recovery phrase on a new Ledger.
Conclusion — Safe Login Protects Your Financial Freedom
Ledger Live is a powerful companion application, but its safety hinges on proper usage and authentication through the hardware wallet.
By understanding the architecture — private keys, cold storage, secure elements, and offline signing — you build a deeper defense against scams.
Authentic software, device-based verification, and offline backups form a multi-layered shield around your assets.
Always follow the official login flow — because your security begins with the path you choose.
By understanding the architecture — private keys, cold storage, secure elements, and offline signing — you build a deeper defense against scams.
Authentic software, device-based verification, and offline backups form a multi-layered shield around your assets.
Always follow the official login flow — because your security begins with the path you choose.